There are several causes for HTTP Strict Transport Security (HSTS) not working correctly. The most common HSTS issues are listed in this article.
Response error: Multiple HSTS headers (number of HSTS headers: 2)
When you see this error the HSTS header has been set twice. The HSTS header should be set only once. This is usually caused by a second HSTS header, added by either your hosting provider or a different plugin. This header is often located in the .htaccess file. Check your .htaccess file for any ‘Strict-Transport-Security’ entries, such entries can be safely removed.
Still having issues? Fill in a support request and we’ll help you figure out what might be going wrong.
How to check if the HSTS header is set
The first thing to check if is the HSTS option has been enabled. To enable HSTS, you can simply enable the setting in Really Simple SSL Pro; which is located under Settings -> SSL & Security -> “Settings” in the top menu bar -> Security Headers -> HTTP Strict Transport Security. If you also want to configure your site for the HSTS preload list, additionally enable the Include Preload and Include Subdomains options, and set the max-age for HSTS to two years.

Note: Be careful before submitting your site to the HSTS Preload list. It means that all subdomains (e.g. sub.domain.com) will be forced over https as well. Removal from the preload list is very difficult, and might not propagate very fast. So even when you’re removed, your site may still be included in the list for months.
You can then test whether the HSTS header is set on your website by entering your domain on scan.really-simple-ssl.com, and check if the HSTS header is returned. If the HSTS header is set, you will see a Strict-Transport-Security block:

If this block appears, the HSTS header is active. If you intend to submit your site to the HSTSPreload list and enabled the Include Preload, Include Subdomains and max-age (two years) options, you will see the Strict-Transport-Security header with a max-age value of 63072000 (two years) and with ‘includeSubdomains; preload‘ added. This means the site is eligible for the HSTS preload list.

If you don’t see a Strict-Transport-Security block, this indicates that the HSTS header is not active. This can have a number of reasons.
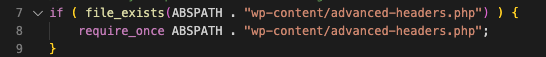
Really Simple SSL Pro sets the HSTS header in a file called advanced-headers.php, located in the /wp-content/ folder. You can open this file with a text editor to verify if it contains the HSTS header:
![]()
If you see the HSTS header in your advanced-headers.php file, but not on scan.really-simple-ssl.com, verify that the wp-config.php file of your site contains a rule similar to the below.
If both of these items are present but you still don’t see the HSTS header in the test results on scan.really-simple-ssl.com, try testing your URL with ?nocache appended (e.g. “your-domain.com/?nocache”). If this does result in the HSTS header appearing in the test results, performing a Clear/Purge All action in your caching/optimization tools and re-saving the settings in those plugins, often helps to correct the results.
If not, we recommend testing whether temporarily disabling these tools and re-scanning your domain on scan.really-simple-ssl.com results in the HSTS header appearing correctly. In some cases, like when using “Disk: Enhanced” mode in W3 Total Cache, a caching plugin completely bypasses PHP and serves static HTML only; which is incompatible with the Security Header functionality in Really Simple SSL.
Error: No HSTS header. Response error: No HSTS header is present on the response
If you see the No HSTS header is present on the response error, the HSTS header hasn’t been set correctly. See ‘How to check if HSTS is set’ to check if the HSTS header is set in your .htaccess file.
‘www.example.com’ is a subdomain. Please preload ‘example.com’ instead
A www. domain is seen as a subdomain. To resolve this error, submit the domain without www.
Example.com (HTTP) should immediately redirect to ‘https://example.com’ (HTTPS) before adding the www subdomain. Right now, the first redirect is to www.example.com
For HSTS to work correctly, the first redirect should be from http:// to https://. Really Simple SSL will add a redirect to https:// by default. This redirect will take priority above other redirects.
If the site redirects to http://www before redirecting to https:// it’s likely there is another redirect set. This redirect should be removed. Often these redirects are located in the .htaccess file. Check your .htaccess file for a redirect to http://www and remove it.
This redirect can also be done by a redirection plugin. Temporarily disable your redirection plugin(s) and check your .htaccess file for a redirect to http://www. This can be fixed by moving the redirect below the Really Simple SSL redirect. Don’t forget to update the redirect to https://www.