This article explains how to configure Vulnerability Detection and Measures in Really Simple Security, and the most important things to consider when doing so.
When you enable Vulnerability Detection and save your settings, a pop-up will appear to configure when a notification should appear, and the plugin will schedule an initial scan to discover vulnerable plugins and themes.
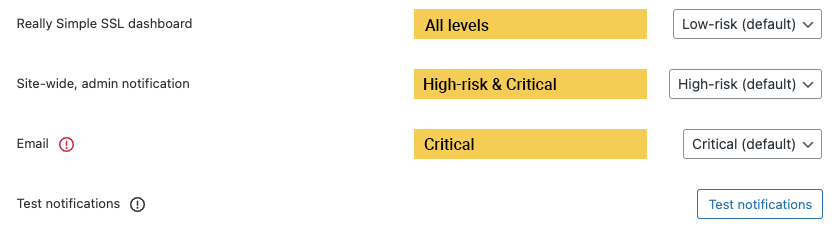
Notifications
You can configure when and how to show the notifications based on the minimum risk level. For example:
- Really Simple Security Dashboard on Low-risk. This means the block progress on the dashboard of Really Simple Security will be used to show a notification for ALL risk levels.
- Site-wide, admin notification on High-risk. This will display a site-wide admin notification for High-risk AND Critical vulnerabilities
- Email on Critical. You will be notified about the discovered vulnerability by email, when a Critical vulnerability is discovered.
The test notifications are used to make sure everything works correctly, so you’re notified accordingly. Emails are sent from your own server and when disabled, can be configured under Settings -> General. If you do not receive an email, please check your server or use a plugin like WP Mail SMTP to make sure deliverability is 100%.
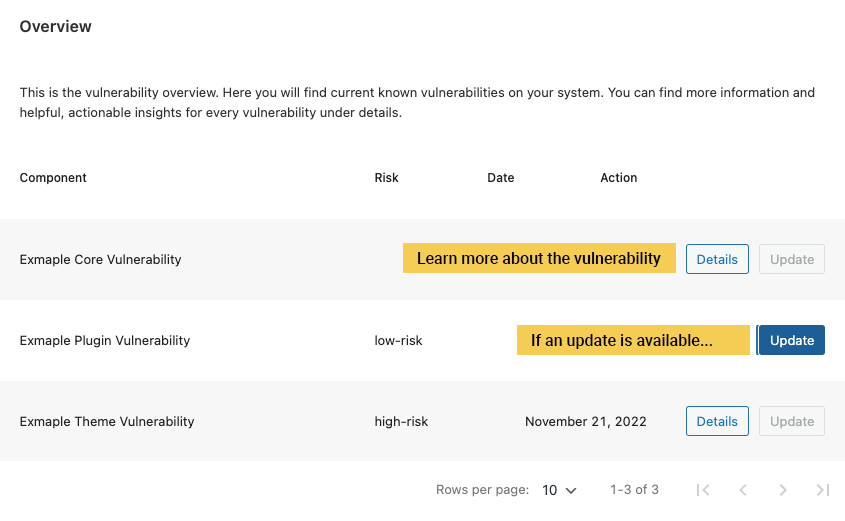
Components
This is an empty block, if you’re lucky. Here you will find information about present vulnerabilities, you can find details about the vulnerability itself, including possible actions.
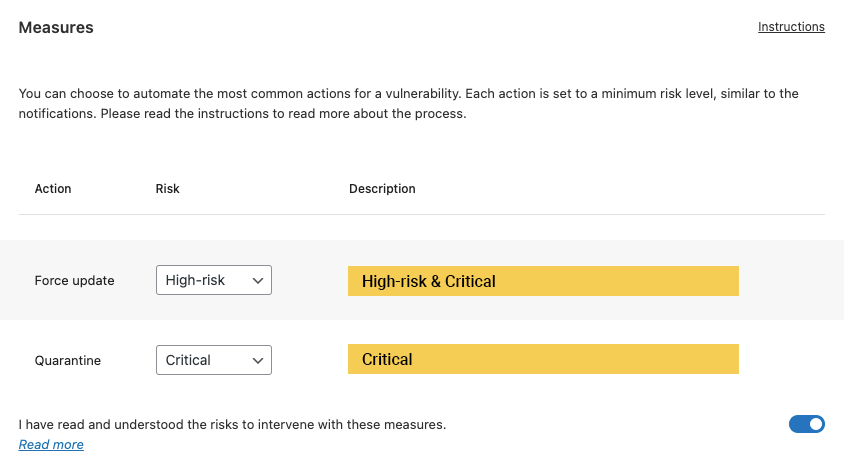
Measures
If you want full peace of mind, you can enable ‘Vulnerability Measures’ in Really Simple Security Pro.
These measures are the most effective way to keep your website from using vulnerable components, as the plugin will:
- Resolve the vulnerability by force-updating the plugin
- Resolve the vulnerability by quarantining the vulnerable plugin
To illustrate the process, it is probably best to provide a real-world example.
In the example below, the plugin has found both a high-risk and a critical vulnerability. This has triggered the Measures feature.
- You will receive an email about the vulnerabilities found. Ideally, you would take manual action, but holidays, time, and clients might get in the way. So we proceed;
- After 24 hours, an update will be forced (when available) on both vulnerabilities.
- It’s either successful, or we try again in another 24 hours. We will let you know.
- If another update round is unsuccessful, the Critical vulnerability will be escalated to Quarantine (deactivation & removal), and the High-risk vulnerability exits the process.
What happens now?
After communicating about the process & actions to the site admin, we are ending the process with a final action.
High-risk vulnerability
The high-risk vulnerability was set to Force update. So at the end of the cycle it is either updated or not. When an update is not available at the end of the process, you will be notified.
Plugins & themes that are in active development will usually release an updated version containing a patch, before the vulnerability becomes public knowledge. A plugin, theme etc that does not successfully patch a vulnerability within 2 weeks, is mostly like no longer actively maintained.
Critical vulnerability
Where the high-risk vulnerability ends the process, the critical vulnerability will be placed in quarantine, and can no longer be executed. You will receive an email when done.
Quarantine means obfuscation and deactivation of the vulnerable plugin. It’s the most effective approach, but will cause a disruption on your website. If it’s a plugin used for calendar booking, it will no longer be available (unless it is re-enabled manually).
If it concerns a WordPress Theme, the theme will be deactivated as well. In short, you will lose the functionality but safeguards the rest of the website.
This is why we highly recommend to mainly use actively developed & well-supported plugins and themes. This goes a long way in ensuring that any discovered vulnerabilities will receive a timely patch.
